OAuth vs. JWT: What's the Difference for Application Development

- Share:





2938 Members
In recent years, two prominent technologies have become widely used in web app security: OAuth and JSON Web Tokens (JWT). While both play a critical role in the authentication and authorization processes, they serve distinct purposes and operate under different principles. This article delves into the specifics of OAuth and JWT, comparing their functionalities, use cases, and how they complement each other in securing web applications.
The JWT is a compact, URL-safe token format primarily used to transmit information between parties securely. It's a JSON object that can encode a variety of claims, such as user identity and attributes. The beauty of JWTs lies in their self-contained nature, meaning the token itself holds all necessary information, which is verified through digital signatures.
To understand JWTs, let's explore their structure, which comprises three parts: header, payload, and signature. The Header typically declares the token type (JWT) and the signing algorithm (e.g., HMAC SHA256). The Payload contains the claims, which could be registered, public, or private claims. Lastly, the Signature is computed by encoding the Header and Payload using Base64URL and then signing it with a secret key.
For instance, consider a JWT token used in a user authentication scenario:
// Header
{
"alg": "HS256",
"typ": "JWT"
}
// Payload
{
"sub": "1234567890",
"name": "John Doe",
"admin": true
}
// Signature
HMACSHA256(
*base64UrlEncode(header) + "." +
base64UrlEncode(payload),
secret)*
This example illustrates a JWT token where the payload carries the subject's identity, user name, and administrative rights. The server can validate this token using the specified algorithm and secret key.
OAuth, specifically OAuth 2.0, is not a token format but an authorization framework. It defines a series of flows, or 'grant types,' which enable a client application to access resources on behalf of a user. OAuth involves obtaining an 'access token,' which the client uses to authenticate requests to a resource server.
OAuth's strength is its versatility in handling different scenarios, from web applications to mobile devices and server-to-server communication. It separates the role of the client (requesting access) from the resource owner (the user) and the authorization server (validating the user and issuing tokens).
Consider a web application that uses OAuth to access a user's data from a social networking service. The flow typically involves:
This process ensures that the user's credentials are not exposed to the web application, thereby enhancing security.
OAuth 2.0 offers various grant types for different scenarios, each designed to provide secure delegated access under specific conditions.
Despite their differences, JWT and OAuth can work together effectively. In many OAuth implementations, the access tokens issued are, in fact, JWTs. This combination leverages both technologies' strengths: OAuth's robust authorization framework and JWT's ability to encode user information and claims securely.
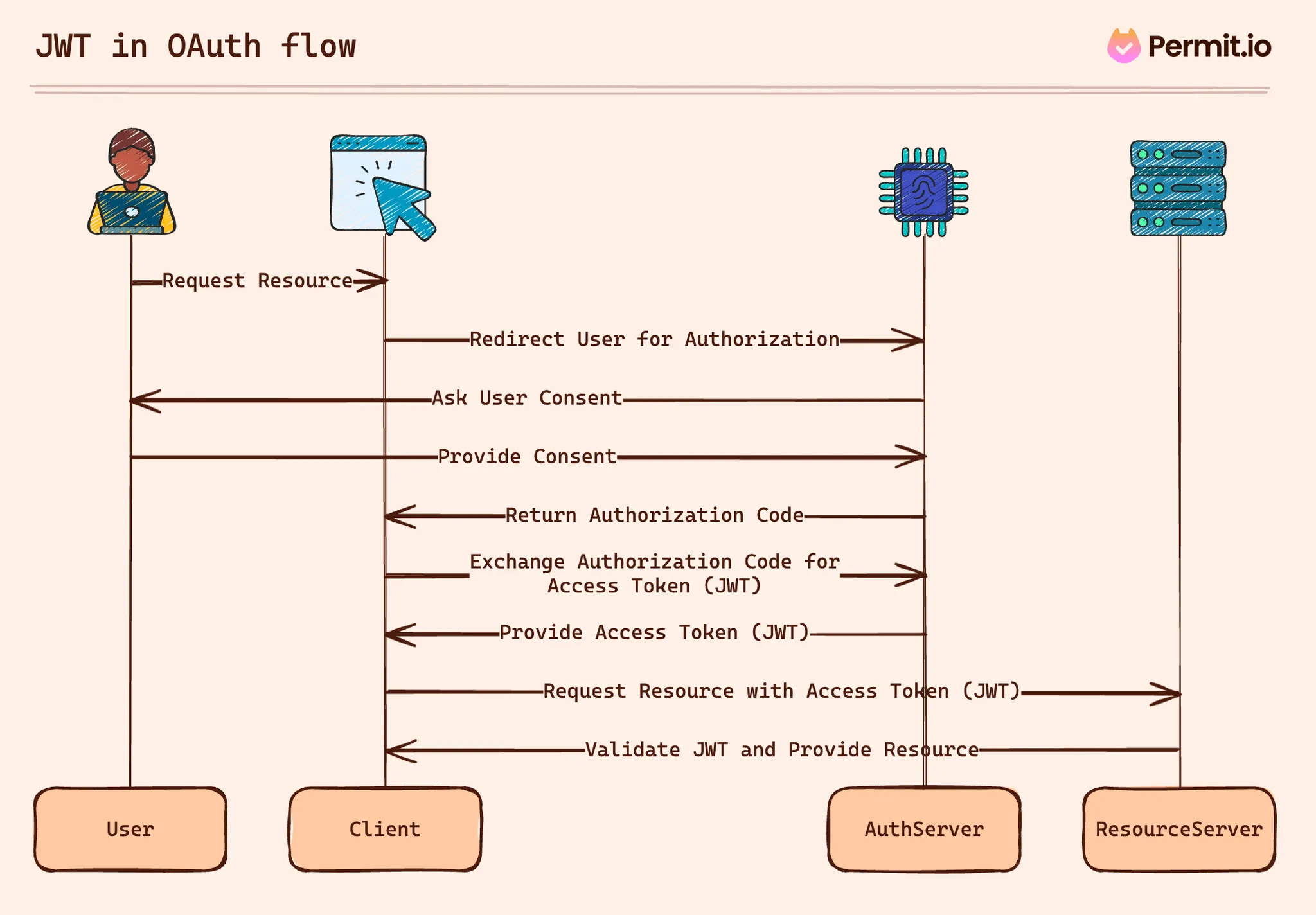
For example, in an OAuth 2.0 flow, once the client receives an access token (which could be a JWT), it can make authenticated requests to the resource server. The server then validates the JWT, ensuring it’s signed and not tampered with, and extracts the user information and permissions encoded within it.
This combination is particularly useful in Single Page Applications (SPAs) and mobile apps, where the stateless nature of JWTs helps maintain user sessions without server-side storage, while OAuth manages the permissions and scopes of what the client can access.
Security Considerations
While both JWT and OAuth provide strong security mechanisms, it's critical to implement them correctly to avoid vulnerabilities:
Another aspect in which JWT and OAuth play an important role is authorization - the stage at which an application decides what a user is allowed or denied access to. In JWTs, token claims can provide important information about the user attributes required for permissions. In OAuth flows, the token scopes provide information about the specific token's desired scopes.
One common misconception regarding JWT and OAuth is their ability to be used as a comprehensive application authorization service. Developers often query the scopes and claims directly in the applications to determine if a user can or cannot perform particular actions. This approach can lead to some serious issues:
To tackle these challenges, scopes and claims must be used in an authorization service that decouples policy from code. An authorization service, Such as Permit.io, should evaluate authorization decisions using scopes and claims as part of a comprehensive permission model that calculates all relevant security factors, allowing you to integrate JWTs and OAuth into your application seamlessly.
Understanding OAuth and JWT is essential for modern web development. While OAuth provides a flexible authorization framework, JWT offers a compact way to represent user information securely. Combined, they form a potent combination for securing web applications, providing strong authentication and fine-grained access control.

Full-Stack Software Technical Leader | Security, JavaScript, DevRel, OPA | Writer and Public Speaker