What is RBAC? Uses and Implementation

- Share:





2938 Members
Role-Based Access Control (RBAC) is a cornerstone of application authorization, so much so that it is often synonymous with the concept of managing user permissions. Its widespread use is not by coincidence; it's due to its fundamental utility and relevance in a wide array of application scenarios. In this article, we delve into the intricacies of RBAC, exploring its basic premises, operational advantages, the challenges it addresses, and those it poses.
RBAC restricts system access to authorized users based on their roles within an organization or a system. Let's consider a common RBAC use case scenario in an application: an e-commerce platform. In such a system, the RBAC rules might define distinct roles like 'Customer', 'Sales Manager', and 'System Administrator', each with varying levels of access and privileges. A 'Customer' may only view and purchase products, whereas a 'Sales Manager' could have additional access to sales data and inventory management tools. The 'System Administrator' role, on the other hand, would have broad permissions, including the ability to modify user roles and access rights.
RBAC operates by assigning users roles that, in turn, have permissions attached to them.
These permissions dictate what actions a user can perform and what resources they can access. This approach streamlines the process of managing user rights, as it is no longer necessary to assign permissions on an individual basis.
Instead, managing access becomes a matter of assigning the appropriate role to a user's account. This structure not only simplifies the setup process but also enhances security by minimizing the risk of inappropriate access grants.
To better understand RBAC, imagine a table of permissions corresponding to different roles within an application. For instance:
Here’s an example of such a table from Permit.io no-code RBAC UI 👇🏻
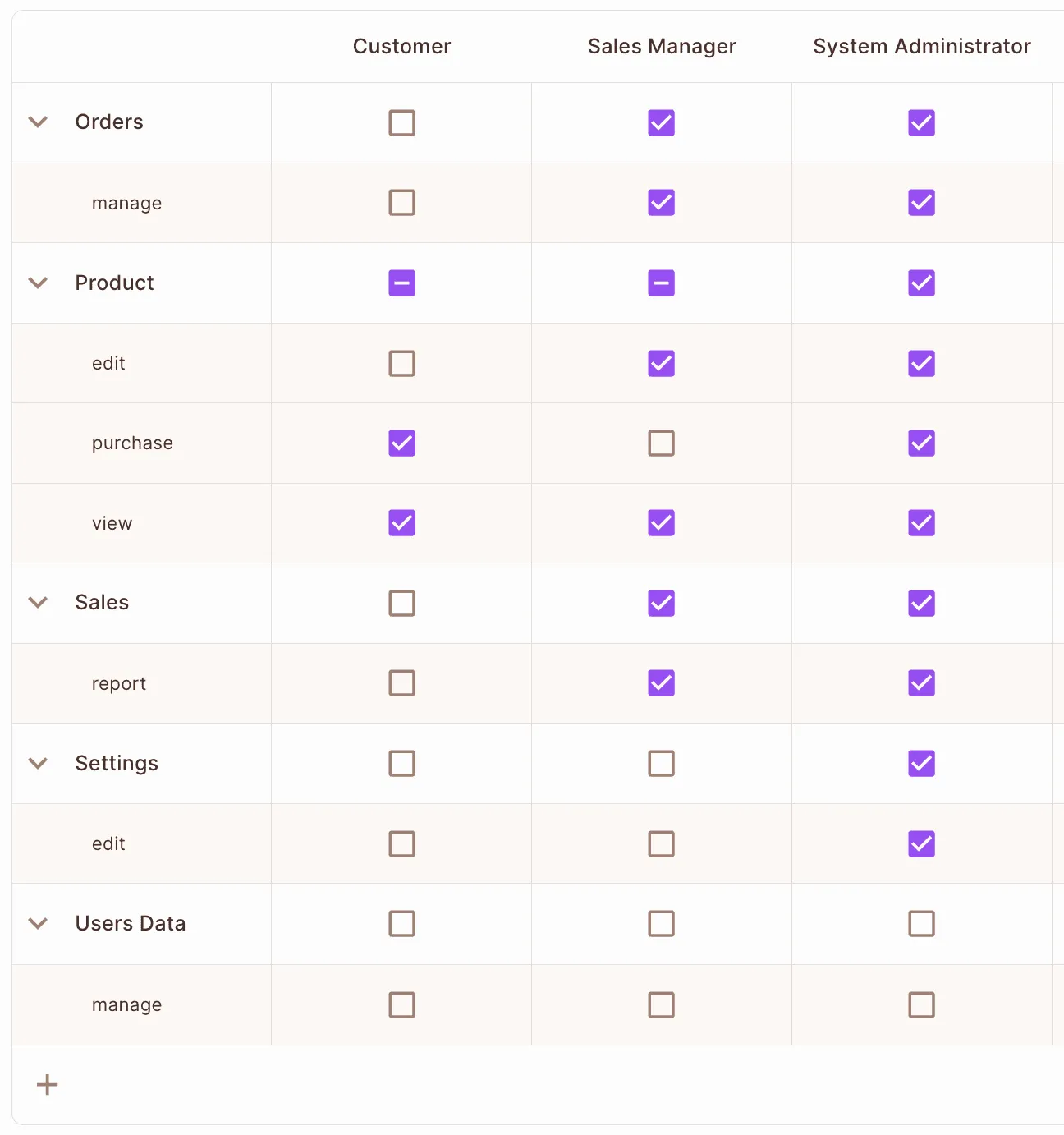
This delineation of roles and permissions exemplifies how RBAC structures access control in a clear, manageable fashion that contributes to both security and efficiency.
The primary advantage of RBAC lies in its simplicity and efficiency. By categorizing users into roles and assigning permissions to these roles, RBAC creates a system that is easy to manage and audit. This streamlined process reduces the likelihood of errors in individual permission assignments. Here are the key benefits:
However, RBAC is not without its challenges. Its simplicity can be a double-edged sword in complex scenarios requiring granular access control.
While advantageous in many scenarios, RBAC's simplicity can pose challenges in situations where fine-grained access control is required. Key challenges include:
While RBAC serves as a good base, alternative models offer better solutions in some scenarios.
Attribute-Based Access Control (ABAC) enhances granularity compared to RBAC by utilizing attributes (e.g., user location, time of access) in addition to roles. While this allows for more detailed access control, it complicates the audit process and requires more configuration effort. ABAC's dynamic nature can adapt to varied and complex scenarios but at the cost of increased system complexity and potential administrative overhead.
Relationship-Based Access Control (ReBAC) extends RBAC's capabilities by considering relationships between entities (e.g., manager-employee). Unlike RBAC, which is not inherently hierarchical and limits inspection to a single resource instance, ReBAC accommodates complex hierarchical structures and relationships. However, authoring and implementing performant decisions in ReBAC can be more complex compared to RBAC, making it suitable for advanced, relation-rich environments.
Policy-Based Access Control (PBAC) integrates well with RBAC, allowing policies to be configured as rules. This approach can be seen as an extension of RBAC, where access control decisions are based on policies that can encompass a variety of conditions and contexts. PBAC provides a framework for creating more dynamic and context-sensitive access control systems, aligning well with applications requiring adaptable and comprehensive access control strategies.
Implementing RBAC effectively requires thoughtful planning and execution. Best practices include:
Read more about RBAC Best Practices
An example of RBAC Policy Code in Cedar Language 👇🏻
permit(
principal in Role::"admin",
action in [
Action::"task:update",
Action::"task:retrieve",
Action::"task:list"
],
resource in ResourceType::"task"
);
While RBAC stands as a fundamental model in application authorization, understanding its limitations and alternatives is crucial for developers aiming to build secure, efficient, and compliant systems. By wisely applying RBAC and its alternatives, you can ensure your applications remain secure, adaptable, and aligned with evolving business requirements.
RBAC is a great authorization solution due to its simplicity and effectiveness, but you should also consider hybrid approaches for more complex scenarios. For a robust and streamlined RBAC implementation, Authorization-as-a-service providers like Permit.io can provide an excellent starting point, offering ease of use and scalability to meet diverse application needs.
Want to learn more about Authorization? Join our Slack community, where thousands of developers discuss, build, and implement access control for their applications.
More RBAC-Related Resources are available here:

Full-Stack Software Technical Leader | Security, JavaScript, DevRel, OPA | Writer and Public Speaker