




2938 Members
As MCP adoption grows, more teams keep running into the same mistake under different names. Some notice that agents are operating on inherited credentials. Some notice that a successful OAuth flow still leaves huge gaps in runtime control. Others realize they can authenticate the human cleanly but still cannot answer what the agent should actually be allowed to do on that human’s behalf.
All of those problems point to the same distinction: MCP auth and agent authorization are not the same thing.
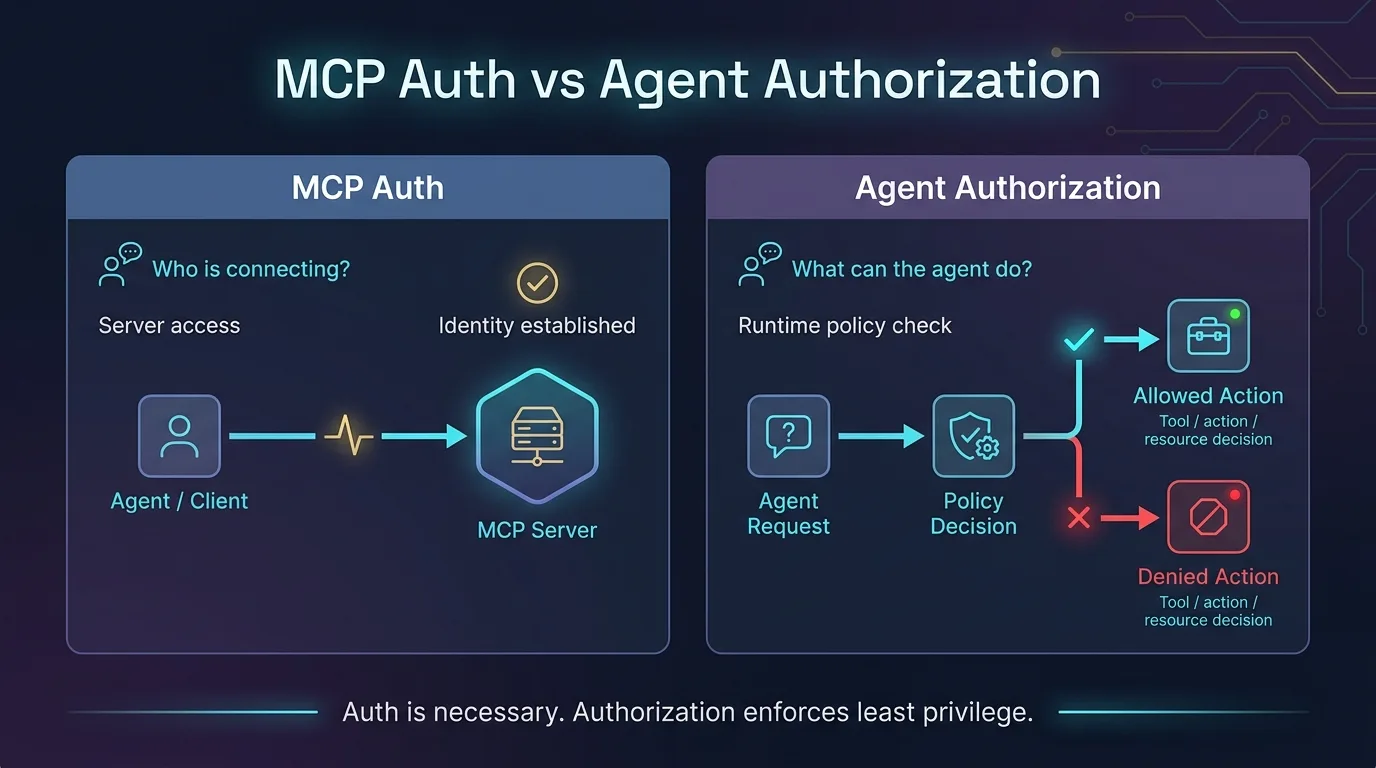
They are related, but they solve different layers of the problem. Authentication answers who connected and under what trust mechanism. Authorization answers what the delegated agent may do, for whom, under which policy, in which context, right now. If a team collapses those into one concept, it ends up with agent workflows that are connected but not truly governed.
The shortest useful version is this: MCP auth gets an entity into the system, while agent authorization decides what that entity may do once it is there. OAuth, SSO, API keys, and similar mechanisms can establish identity and session legitimacy. They do not, by themselves, define the ongoing scope of agent behavior.
That distinction has always mattered in software, but it matters much more in agent systems because the acting entity is delegated and dynamic. The agent is not just logging in for itself. It is often operating through permissions derived from someone else, across tools that vary in risk and intent.
So when someone says “we already solved agent security because we use OAuth,” what they usually mean is that they solved connection establishment. They have not necessarily solved runtime authorization.
Part of the confusion comes from how application security evolved. For years, many systems got away with a relatively simple mental model. Authenticate the user, issue a token, let the application trust that token for the rest of the session, and maybe check a few roles on the way through. That works well enough when the acting subject is a human using a bounded interface.
Agent systems stretch that model quickly. Once an agent can discover tools, chain actions, reuse context, and interact with multiple downstream systems, the old assumption starts to crack. A successful authentication event at the start of the session does not tell you whether the next tool call should be allowed. It only tells you that some identity was admitted into the flow.
That is why the gap becomes visible so quickly in MCP. Teams reach for auth because it is familiar, but what they actually need next is an authorization model that understands delegation.
MCP auth still matters. It is the mechanism that verifies who is connecting to the gateway or server and under which authentication flow. It can establish that the human is real, that the client is using a recognized session, and that the connection belongs to a trusted trust boundary.
That is foundational. Without it, the rest of the system becomes meaningless. But auth is still just the entry point. It authenticates the actor or session. It does not automatically define the scope of that actor’s behavior across tools, actions, consent windows, or downstream resources.
That is why saying “OAuth solved it” feels satisfying at first and incomplete five minutes later.
Agent authorization begins where auth stops. It asks what this agent may do on behalf of this human in this context, under this consent scope, against this tool, right now. That is a different question from whether the user or client authenticated successfully.
This is where delegated identity becomes important. A human may be entitled to a certain set of actions. The agent acting for that human may deserve a narrower set. The narrowed set may change depending on the tool, the workflow, the time window, or the sensitivity of the action. Authorization is where the system expresses those differences explicitly.
In a well-governed MCP deployment, the gateway evaluates those decisions at runtime. It does not rely only on what happened at login time. It uses identity, consent, tool metadata, trust tier, and policy to determine whether the action should be allowed now.
OAuth is useful for delegated access, but people often overestimate what it provides. It can help authorize a client to obtain or use tokens under a recognized flow. It does not automatically encode all the business and security logic required for agent behavior after the token exists.
That is the key limitation in MCP systems. Once the agent has a valid authenticated path, the hard part is no longer proving the session was initiated correctly. The hard part is deciding whether each downstream action still fits the delegated intent of the human, the approved consent scope, and the organization’s trust model.
A token can tell you that access was granted. It usually cannot tell you whether the current action should still be allowed under the evolving context of an agent session.
This becomes clearer when you look at the questions security teams eventually ask. Which human delegated authority to this agent? What tools were in scope for that consent? Was the action read-only, transactional, or destructive? Was the session still inside its valid trust window? Did the behavior drift mid-session in a way that should trigger revocation or escalation?
Those are not authentication questions. They are authorization and governance questions. A strong auth system may feed data into them, but it does not answer them alone.
This is the point where many early MCP deployments realize they are missing the control layer they actually need.
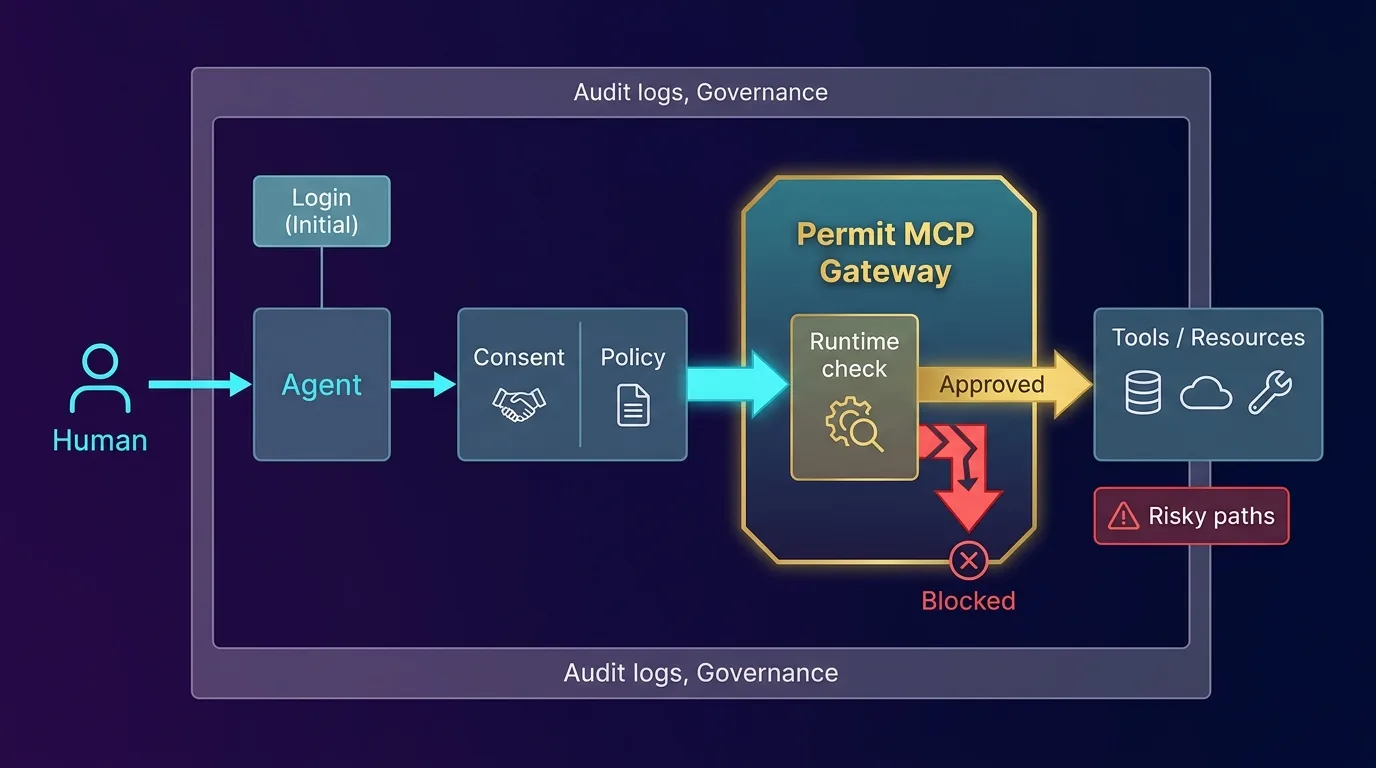
A more complete model usually has four elements. First, the human and the agent need to be bound together clearly enough that the delegated relationship is explicit. Second, the system needs to capture consent so it can explain why the agent was allowed to use certain tools and for how long. Third, policy has to evaluate actions at runtime rather than treating the initial authentication as the final trust decision. Fourth, the resulting decisions need to be visible enough for audit and incident response.
Once those pieces exist, auth and authorization stop competing with each other. They become successive layers in the same system. Auth establishes the subject. Authorization governs the behavior. Audit and guardian logic help the organization respond when the behavior drifts.
That is a much stronger story than “we use OAuth.”
The difference between auth and authorization may sound academic until agents start touching real systems. But once the agent can reach internal tools, customer systems, financial actions, or administrative workflows, the distinction becomes operational very quickly. A connected but under-governed agent is often more dangerous than a disconnected one, because the team assumes the security problem is already solved.
That is why production MCP systems need an explicit authorization layer at the gateway or equivalent control point. The organization needs somewhere to ask, in real time, whether this particular action should happen. Otherwise the only meaningful control event happened at the beginning of the session, long before the risky behavior arrived.
MCP auth and agent authorization belong in the same architecture, but they should never be treated as the same control. Authentication proves who entered the system. Authorization decides what the delegated agent may do after entry. OAuth is part of the answer, but it is not the whole answer.
That is the practical reason Permit MCP Gateway emphasizes delegated identity, consent, policy evaluation, and runtime enforcement rather than stopping at connection setup. The organizations that get this distinction right are the ones that move from “agents can connect” to “agents can operate under control.”
Co-Founder / CEO at Permit.io