




2938 Members
If you are comparing an MCP gateway vs MCP proxy, the practical answer is simple: a proxy helps MCP traffic reach the right upstream service, while a gateway governs who the agent is, on whose behalf it is acting, what it may do, and how that decision is recorded. In local demos, the two can look similar. In production, they solve different problems.
That distinction matters because MCP is not just another integration pattern. The Model Context Protocol (MCP) gives agents a structured way to discover tools and invoke them. Once those tools touch tickets, code, customer data, or internal systems, the problem stops being just connectivity. It becomes a trust and control problem.
An MCP proxy is usually a transport component. It forwards requests, terminates TLS, normalizes access, or hides topology. An MCP gateway is the policy and control layer that sits between AI agents and the tools they invoke. It is where identity, consent, authorization, and auditability become enforceable instead of implied.
That is why the difference is not branding. It is the difference between making MCP work and making MCP governable.
A proxy is still useful. Many teams need one first. But once an AI agent acts on behalf of a human, the system has to represent delegated authority explicitly. That requires more than safe routing.
The table below is a good shorthand, but it only works if you read it as an operational difference rather than a product category debate.
| Component | Primary job | What it answers well | Typical limit |
|---|---|---|---|
| MCP proxy | Connectivity, mediation, and transport handling | How does the client reach the MCP server safely? | Usually knows little about delegated identity, consent scope, or per-tool policy intent |
| MCP gateway | Identity, consent, authorization, audit, and runtime control | Should this agent be allowed to perform this tool action right now? | Needs a real trust model, not just forwarding logic |
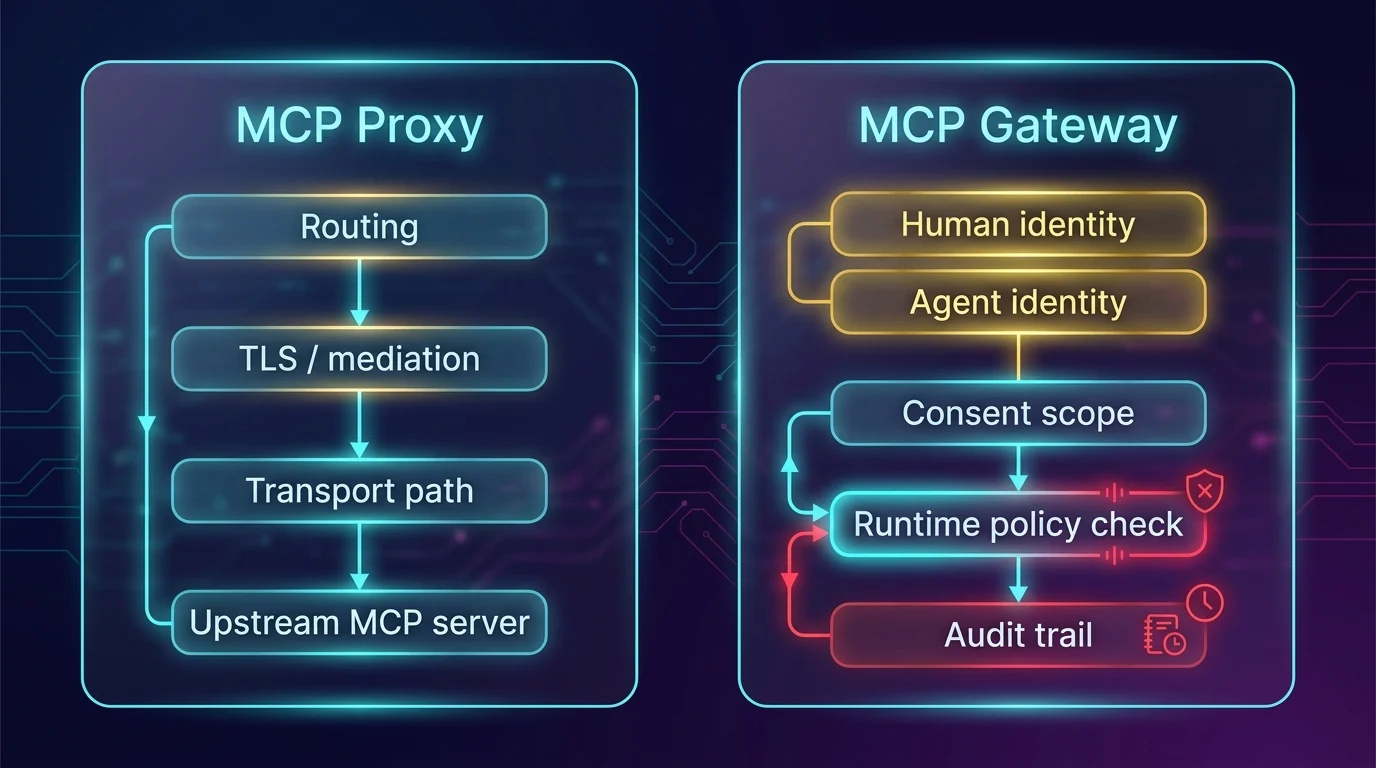
The comparison is straightforward in prose, but the operating boundary is what matters: the proxy mainly owns the transport path, while the gateway owns the delegated trust decision and the evidence around it.
The confusion is understandable because the early architecture often looks the same from a distance. There is a component in the middle, traffic flows through it, and both the proxy and gateway can mediate access to upstream MCP servers.
That similarity breaks down once the system leaves the lab. Teams start with a lightweight wrapper because it is the fastest path to exposing a tool. Then they add more tools, more users, and more risk. At that point, the question is no longer whether the request can be forwarded. The question is whether the delegated action should happen at all.
This is where terminology starts shaping architecture. If a team thinks it only needs a proxy, it will usually optimize for connection handling, request translation, and maybe header-level controls. It will not naturally build the deeper control path required for agent identity, consent capture, runtime policy evaluation, and audit evidence.
The result is a familiar production failure mode: the system works technically, but nobody can explain why an agent was allowed to do something sensitive.
This is not a case against proxies. An MCP proxy is often the right tool when the real need is network mediation. It can standardize how clients reach MCP servers, smooth over infrastructure boundaries, centralize TLS and routing concerns, and reduce direct exposure of internal services.
That is real operational value. If your environment is low risk, local, or mostly concerned with protocol plumbing, a proxy may be enough. Not every MCP deployment starts with a full trust and governance layer.
The problem is that an MCP proxy usually stops at the transport boundary. It can prove that a request moved through the right path. It usually cannot explain the delegated meaning of that request.
In MCP systems, that missing meaning matters more than in older integrations because the agent is not just a passive caller. The agent discovers tools, accumulates context, chains steps together, and can drift from a benign read to a risky action in the same session.
An MCP gateway becomes necessary when the trust model itself must be enforced. The moment an agent acts on behalf of a human, the architecture needs to bind the human identity, the agent session, the granted consent scope, and the requested tool action into one decision path.
That is the real line between gateway and proxy. A proxy can carry a valid request. A gateway can evaluate whether the request belongs inside the delegated authority of that agent at that moment.
A production gateway usually becomes the place where several concerns meet:
Those are not transport features. They are governance features.
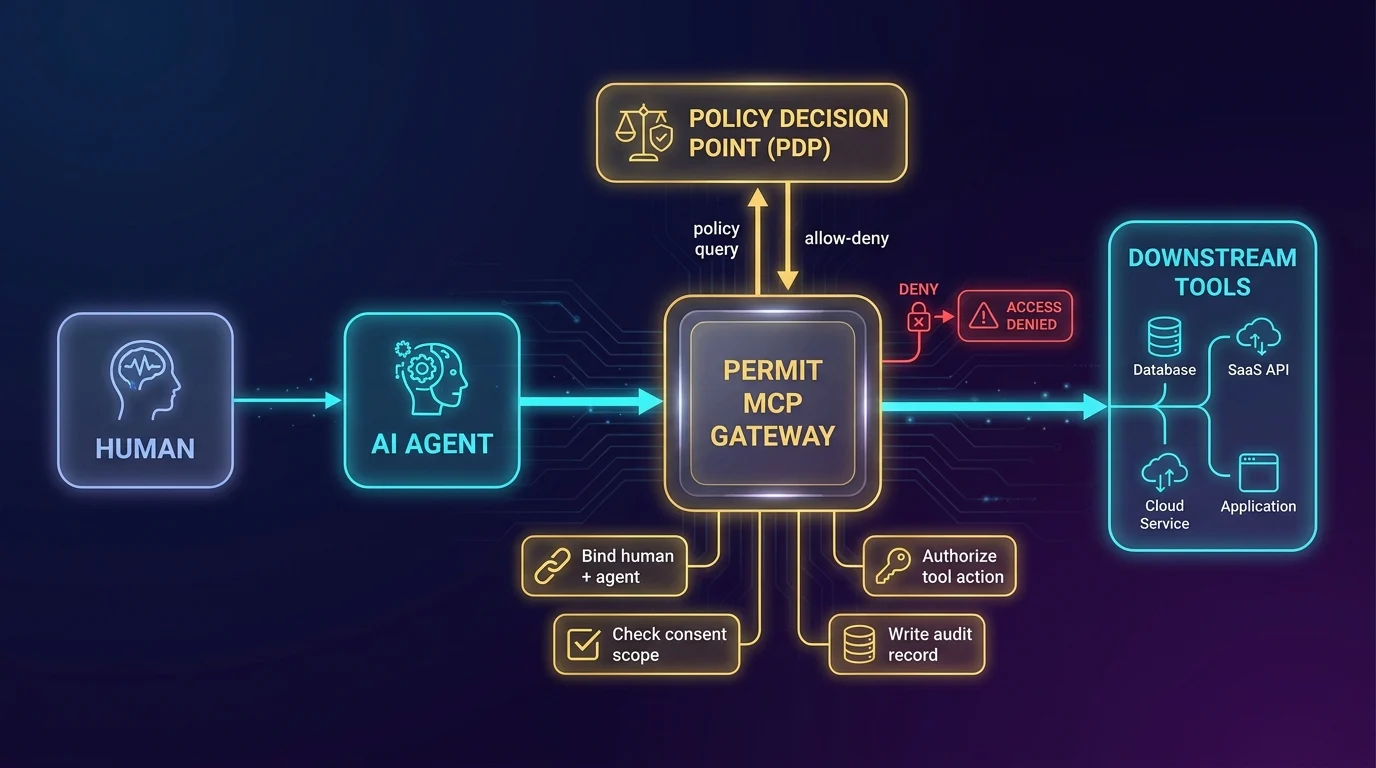
This is the architectural shift in one picture: the gateway is where the system binds the human to the agent session, checks the current consent scope, asks policy whether the tool action is allowed, and records the decision before the request reaches downstream tools.
Older service integrations often relied on a simpler trust model: authenticate once, establish a session, and assume the caller stays inside expected behavior. MCP makes that model weaker because agents are dynamic. They do not just call one known endpoint with one stable intent. They interpret context, choose tools, and act across changing workflows.
That means the control point has to evaluate more than the initial connection. It has to reason about the relationship between the human, the agent, the current action, and the downstream tool. In practice, that is what teams mean when they say they need runtime control for AI agents.
A citation-friendly way to frame it is this: an MCP proxy helps an agent reach a tool, while an MCP gateway helps the organization decide whether the agent should be allowed to use that tool in this context right now.
That difference is what security reviews, legal reviews, and incident response teams eventually care about.
The easiest way to tell whether you need a gateway is to ask a few uncomfortable production questions.
Can the system bind an agent session to a real human identity? Can it show what consent was granted, for which tools, and for how long? Can it evaluate each tool action at runtime rather than relying only on a token minted earlier? Can it produce audit records that explain the decision, not just the connection? Can it propagate enough trust context downstream that other systems are not blind once the request leaves the edge?
If the answer to those questions matters, you are already in gateway territory.
That is also why teams often "grow into" a gateway even if they started with a proxy. Security asks for least privilege. Compliance asks for records. Platform teams ask how policy decisions remain consistent across services. Incident response asks what happens when agent behavior drifts mid-session. A transport component alone cannot answer those questions cleanly.
Permit’s view is that the hard production problem is not routing. It is delegated control. That is why the product language around Permit MCP Gateway centers on authenticating humans, identifying agents, collecting consent, and governing tool access in real time.
The surrounding Permit stack matters here too. The site and product materials consistently describe low-latency PDP deployment close to the workload, hybrid and in-VPC deployment patterns, decision logging, and audit visibility. That is the shape of a gateway architecture: the control point is connected to policy, identity, and evidence, not just forwarding.
In that model, the gateway is where the organization can enforce least privilege for agent actions and keep the resulting decisions visible enough for security teams, operators, and auditors. A proxy can help with the packet path. A gateway has to own the decision path.
A proxy is usually enough when the deployment is narrow in scope and low in risk. That might mean local experimentation, internal tooling with no delegated user authority, or a setup where the main requirement is simply to expose an MCP server through a safer network boundary.
A gateway becomes the better description when the environment includes real delegated authority. That usually means agents touching SaaS systems, internal business tools, customer data, regulated workflows, or multi-step operations where the blast radius is larger than a single request.
A useful rule of thumb is this: if failure would lead someone to ask for identity proof, consent evidence, authorization logic, or audit records, the architecture is no longer just about proxying.
An MCP proxy mainly handles connectivity and transport mediation between an MCP client and an MCP server. An MCP gateway adds governance: identity binding, consent, runtime authorization, auditability, and policy enforcement for tool actions. In production, the gateway is the control point for delegated trust.
Yes. In practice, many components called "proxies" gradually accumulate gateway behavior. Once they start evaluating identity, consent, policy, or per-tool permissions, they are no longer solving only a transport problem.
No. For local development, low-risk internal usage, or simple transport mediation, a proxy may be sufficient. You usually need gateway behavior when agents act on behalf of users against real systems, sensitive data, or regulated workflows.
AI agents are dynamic. They discover tools, chain actions, and change behavior based on context. That makes "authenticate once and trust the rest" much weaker. A gateway gives the system a place to evaluate each action in context instead of relying only on the initial connection.
If you only need to connect an MCP client to an MCP server, a proxy may be enough. But if your agents touch real business systems, carry delegated user authority, or need least-privilege control with auditability, then the real requirement is a gateway whether you call it that or not.
That is the operational answer to MCP gateway vs MCP proxy. A proxy helps traffic move. A gateway helps trust survive contact with production.
Co-Founder / CEO at Permit.io