




2938 Members
Identity and access management (IAM) is the processes and technologies used to manage the identities of users and the access they have to different systems and resources. IAM can be divided into three main parts - authentication (verifying a user's identity), authorization (granting or denying access to resources), and identity management (creating, updating, and deleting identity records and associated information). IAM systems are often used to improve security, simplify access management, and reduce the risk of unauthorized access to sensitive data or systems. IAM works like a waterfall:
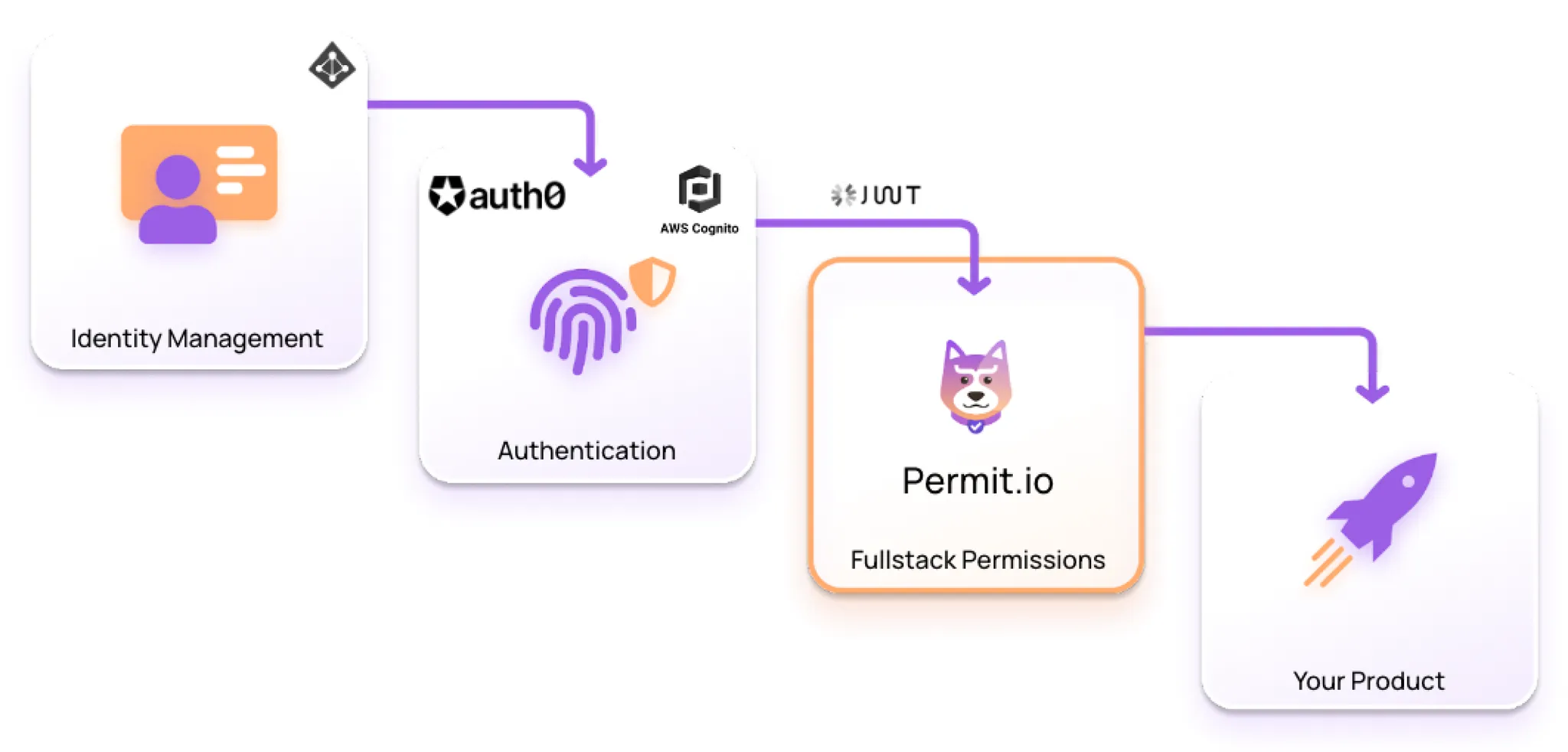
Information flows from the organization side to products used by the organization, starting at the identity provider to authentication at a product’s gateway, and finally to authorization within the product itself.
Let’s Zoom in on each of these —
Identity management solutions help organizations to securely manage the identities of their users and control access to their applications and resources. Identity providers and the identity management process, in general, act as the main source of truth for Authentication and Authorization.
Leading Identity management services include: Okta, Microsoft Azure Active Directory, OneLogin, Ping Identity, Google Identity Platform
Key Identity management Buzzwords:
Single sign-on (SSO): A system that allows users to log in to multiple applications using a single set of credentials. This can make it easier for users to access the resources they need, and it can also reduce the number of passwords that need to be managed and remembered.
Identity provider (IdP): An identity provider is a service that manages the identities of users and provides authentication services. This might be a separate service, or it might be integrated into other systems.
Federation: Refers to the process of linking different identity systems so that users can use the same credentials to access multiple systems. This can be useful in situations where multiple systems need to share user information, but each system has its own authentication mechanism.
SAML (Security Assertion Markup Language): A standard for securely exchanging authentication and authorization data between different systems. It is often used in enterprise environments to enable single sign-on across multiple applications. SAML is one of the main protocols authentication services would connect to Identity providers.
LDAP (Lightweight Directory Access Protocol): A protocol for accessing and managing directory information over a network. It is often used for authentication and authorization in enterprise environments.
The process of verifying a user's identity. This is typically done by requiring the user to provide some kind of credentials, such as a username and password, a fingerprint, or a facial recognition scan.
Leading authentication services include: Auth0, AWS Cognito, SuperTokens, FusionAuth, Magic.link, Stych, Descope.
Key Authentication Buzzwords:
OAuth: OAuth is an open standard for authorization (but de-facto powers a lot of authentication) that allows users to securely access resources on one site using the credentials of another site. OAuth is often used to allow users to log in to third-party applications using their Google, Facebook, or other social media accounts.
OpenID Connect: OpenID Connect is a protocol that builds on top of OAuth to provide authentication as well as authorization. It allows users to securely log in to a web application using their existing credentials from another site.
Multi-factor authentication (MFA): Multi-factor authentication is a security system that requires users to provide multiple pieces of evidence to prove their identity. This might include something they know (like a password), something they have (like a security token), and something they are (like a biometric factor like a fingerprint or a facial recognition scan).
JSON Web Tokens (JWTs): JWTs are a compact, URL-safe way of representing claims to be transferred between two parties. They are often used for authorization and can be signed using a secret key or a public/private key pair. It is the main connection point between authentication and authorization solutions.
Passwordless authentication: a method of authentication that does not require users to enter a password in order to access a system or service. Instead, users are authenticated using other methods, such as a biometric factor (like a fingerprint or facial recognition), a security token, or a one-time code sent to their email or mobile device. It is becoming increasingly popular as a way to improve security and user experience (by reducing dependency on stupid passwords 😅)
WebAuthn: is a web standard that defines an API for performing authentication using various authentication methods. This includes methods like biometric authentication (using a fingerprint or facial recognition), security keys (using a hardware token), and other methods that are more secure and user-friendly than traditional password-based authentication.
The process of granting or denying access to resources based on a user's identity and the permissions that have been assigned to them. This is typically done by comparing the user's credentials against a set of rules or policies to determine what they are allowed to access.
Leading Authorization services include: Permit.io, AuthZed, Ory Keto, Styra DAS
Key Authorization Buzzwords:
Role-based access control (RBAC): The bread and butter of access control; almost every product developer gets here - thanks to its simplicity, it has become quite popular and common. Role-based access control is a method of access control that assigns permissions to users based on their role within an organization. For example, an administrator might have more access than a regular user.
Attribute-based access control (ABAC) is a method that uses attributes (or "properties" of a user or resource) to determine whether a user is authorized to access a particular resource. This is in contrast to other forms of access control, such as role-based access control (RBAC) or discretionary access control (DAC), which use fixed roles or permissions to determine access. ABAC allows for more fine-grained and flexible access control, as it allows permissions to be based on multiple attributes and dynamically evaluated. For example, a user might be granted access to a particular resource if they have a certain role and are accessing the resource from a specific location at a specific time of day.
Relationship-based access control (ReBAC) is a method of access control that takes into account the relationships between different users and resources when determining access permissions. This is in contrast to (RBAC), which assigns permissions based on a user's role within an organization, or discretionary access control (DAC), which assigns permissions based on the user's individual permissions. ReBAC is more powerful than RBAC but can often be more limited when compared to ABAC. ReBAC is perfect for describing groups, hierarchies, and forms of cascading or nested relationships. The most classic example is file systems, where access to a folder implicitly grants access to anything nested under it.
Policy as code: the practice of defining and managing access-control policies using code. This allows policies to be managed and enforced using the same tools and processes that are used for managing and deploying software. This makes it easier to track changes to policies over time, to roll back changes if necessary, and in general, to enjoy the well-thought-through best practices of the world of code - e.g., Gitops.
OPA (Open Policy Agent): A popular open-source (CNCF project) policy engine that enables developers to externalize and manage their policies in a uniform and predictable way. OPA provides a high-level declarative language (Rego) for specifying policies, as well as an engine for enforcing those policies at runtime.
OPAL (Open Policy Administration Layer) - is an open-source project to manage multiple instances of OPA in a real-time, event-driven fashion, delivering the policy and data each agent needs (and only those it needs).
Google Zanzibar: a white paper published by Google describing how they use ReBAC via a graph-based system to manage permissions at scale for products with high volume usages (more than tens of million users) such as Drive and Youtube. The whitepaper, which didn’t include the source code - unleashed a wave of clones, none of which to date has actually fully implemented the offering.
Still confused? Want to learn more about IAM? Join our Slack community, where there are hundreds of devs building and discussing IAM.
Co-Founder / CEO at Permit.io